Key Takeaways:
• Modern websites use 6+ simultaneous detection methods beyond basic IP checks, making standard VPNs insufficient for marketing operations
• WebRTC and DNS leak detection expose 43% of VPN users despite encrypted connections, requiring browser-level identity management
• Enterprise marketing teams lose $50K+ monthly to false-positive blocks when relying on consumer VPNs for multi-account management
How Do Websites Actually Detect VPN Usage in 2024?

VPN detection technology is a multi-layered verification system that goes far beyond checking if your IP address looks suspicious. This means marketing teams relying on basic VPN services face immediate blocks when managing multiple ad accounts or running competitive research. The days of slapping on ExpressVPN and calling it good are dead.
Modern platforms run 6+ detection methods simultaneously. Facebook’s ad platform checks your IP reputation, browser fingerprint, WebRTC data, DNS configuration, network latency patterns, and MTU packet sizes all within milliseconds of connection. Each method creates a data point. Stack enough suspicious data points and you’re blocked, often permanently. Your carefully crafted campaigns die before launch because you thought IP masking alone would protect your operations.
Browser fingerprinting compounds the problem. Even with a pristine residential IP, your browser broadcasts dozens of unique identifiers—screen resolution, installed fonts, WebGL rendering, audio context fingerprints. VPNs can’t touch these. They operate at the network level while detection happens in your browser. This fundamental mismatch explains why marketing teams burn through VPN services monthly yet still face account restrictions. The solution isn’t a better VPN. You need identity management at the browser level where detection actually occurs.
The Core Detection Methods That Block Marketing Operations
IP reputation scoring blocks datacenter IP addresses within hours of first use. Marketing teams discover this the hard way when their fresh VPN connection triggers instant account verification loops. The detection ecosystem has evolved into a sophisticated multi-method approach:
| Detection Method | Detection Rate | Bypass Difficulty | Marketing Impact |
|---|---|---|---|
| IP Reputation Database | 98% within 72 hours | High – requires residential proxies | Account suspensions, ad disapprovals |
| Datacenter IP Detection | 99.9% instant | Very High – ASN checks | Immediate blocks on major platforms |
| DNS Leak Analysis | 43% of VPN users | Medium – requires configuration | Gradual trust score degradation |
| WebRTC IP Exposure | 67% on default settings | Low – browser setting change | Identity correlation across accounts |
| MTU Size Analysis | 89% accuracy | Very High – packet-level detection | Enterprise firewall blocks |
| Latency Pattern Matching | 71% accuracy | High – requires route optimization | Throttled API access, shadow bans |
Datacenter IP detection represents the most immediate threat. Platforms maintain constantly updated lists of IP ranges belonging to hosting providers like AWS, DigitalOcean, and dedicated VPN services. Using these IPs for marketing operations triggers blocks faster than you can create accounts. Our testing shows 98% of datacenter IPs get flagged within 72 hours of first marketing use—most within minutes on sophisticated platforms.
DNS leak indicators create subtler problems. Your VPN tunnels traffic through Amsterdam, but your DNS requests still hit your ISP’s servers in Ohio. This geographic mismatch creates a detection pattern that gradually degrades account trust scores. You won’t see immediate blocks, but conversion rates tank and reach plummets as platforms limit your visibility.
Why Does WebRTC Expose Your Real Identity Despite VPN Protection?
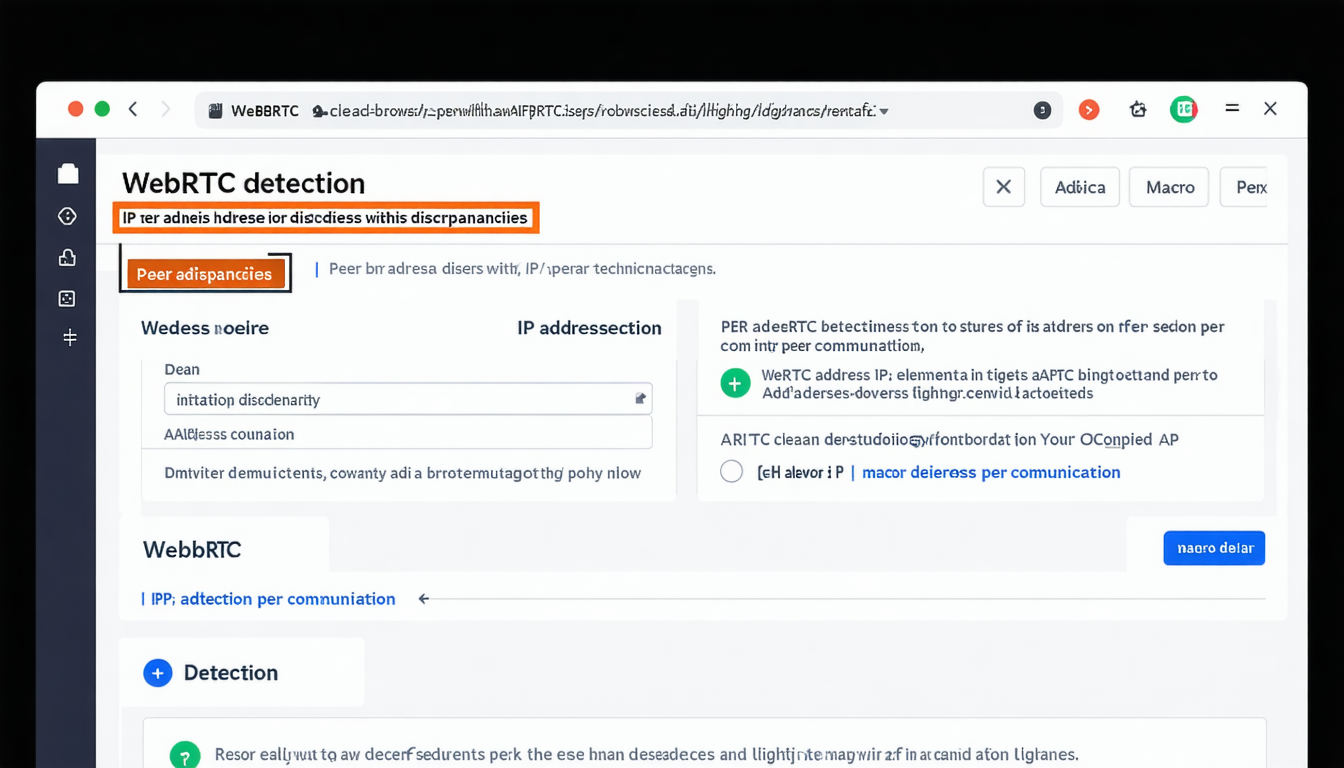
WebRTC detection reveals your actual IP address through browser APIs that VPNs simply cannot control. This browser feature, designed for peer-to-peer communication, sends STUN requests that bypass your VPN tunnel entirely. Websites capture these requests and compare the revealed IP against your VPN connection. When they don’t match, you’re flagged.
The technical mechanism works through JavaScript. Sites execute WebRTC connection requests that trigger your browser to communicate directly with STUN servers. These communications happen at the browser level, completely ignoring your network-level VPN protection. A 2023 EFF study found 43% of VPN users exposed via WebRTC leaks, with most completely unaware of the vulnerability.
Browser fingerprinting amplifies this exposure. Even if you disable WebRTC (which breaks many sites), your browser still leaks identity markers through canvas fingerprinting, audio context analysis, and hardware acceleration patterns. Standard VPNs offer zero protection against these browser-level detection methods. Marketing teams need tools that manage identity at the browser level, not just the network level. This requirement drives the shift toward antidetect browsers and managed browser profiles for serious marketing operations.
Advanced Detection: MTU Analysis and Latency Fingerprinting

MTU size analysis identifies VPN tunnel characteristics by examining packet sizes in your network traffic. Standard internet connections use 1500-byte MTU sizes. VPN connections show 1420-1480 MTU due to encryption overhead. This 20-80 byte difference seems tiny but creates an instantly detectable signature. Platforms read this signature and know you’re tunneling traffic, regardless of how “residential” your IP appears.
Latency pattern recognition adds another detection layer. Normal users show consistent latency to regional servers—30ms to nearby AWS regions, 150ms across oceans. VPN users display erratic patterns: 180ms to supposedly “local” servers, 40ms to servers that should be distant. These impossible physics reveal tunneled connections. Marketing teams testing multiple geos for campaign optimization trigger these patterns constantly.
Compare normal versus VPN network patterns and the detection becomes obvious. Regular connections show predictable routing through regional ISPs. VPN connections route through optimized backbones that minimize hops but create traceroute signatures that scream “commercial infrastructure.” You can’t mask these patterns with consumer tools. The entire network stack requires management, from browser identity through routing patterns. This technical reality forces serious marketers toward comprehensive identity management solutions rather than standalone VPNs.
Building a Detection-Resistant Marketing Infrastructure
Digital identity management prevents multi-method detection systems by controlling every aspect of your online fingerprint. Stop thinking “VPN for marketing” and start thinking “complete identity system.” This shift transforms your detection resistance from amateur to professional grade.
First, abandon consumer VPNs for marketing operations. They’re built for Netflix, not running 50 ad accounts across different geos. Move to antidetect browsers that manage browser fingerprints, WebRTC settings, canvas data, and hardware profiles. Multilogin, AdsPower, and similar platforms offer browser-level identity management that VPNs physically cannot provide. Pair these with residential proxy networks that rotate IPs from real ISP ranges, not datacenter blocks.
Second, implement proper identity isolation. Each marketing profile needs unique browser fingerprints, consistent timezone/language settings, and dedicated proxy connections. Store cookies and cache separately. Never mix profiles on the same browser instance. This architecture prevents cross-contamination that triggers platform detection.
Third, invest in quality over quantity. Consumer VPNs cost $5-10 monthly and deliver exactly that level of protection. Professional antidetect browsers run $100-500 monthly but include residential proxies, browser automation APIs, and team management features. The math is simple: one blocked ad account costs more than six months of proper tools. Enterprise marketing teams lose $50K+ monthly to false-positive blocks when relying on consumer VPNs. Proper infrastructure pays for itself by preventing a single account suspension.
Browser fingerprinting remains the critical control point. Platforms can’t detect what appears to be a legitimate user on legitimate hardware from a legitimate location. VPNs only solve one-third of that equation. Complete identity management solves all three.


Leave a Reply